Tag: Security Land
Top Stories
Man vs. Machine: Will AI Replace Cybersecurity Professionals?
The rise of AI in cybersecurity signifies a new era in our collective defense against cyber threats.
[In-Depth Guide] – The Basics of Packet Firewall
Popular firewalls are, in essence, a class of intermediate router devices engineered to violate the fundamental design of an intermediate…
Android: Debugging and Analyzing Vulnerabilities
Chapter 1 - Android - Debugging and Analyzing Vulnerabilities It’s very difficult—arguably impossible—to create programs that are free of bugs.…
Several Android Apps Are Sharing Your Data to Third Parties
Research claims that several Android apps have “alarming” privacy holes – enabling mobile apps to take and share screenshots and…
How Technology Impact Digital Forensics
Digital Forensics - An art form lacking broad scientific standards Forensics is changing in the digital age, and the legal…
Crypter Handbook – Part 1
Learn Crypter from scratch. Crypters are programs created in order to "obfuscate" (hide) the source code from a file. They…
New Research Can Identify Extremists Online
Finding Extremists Online New research has found a way to identify extremists, such as those associated with the terrorist group…
North Korean hacker officially charged for the WannaCry attacks
Park Jin Hyok, North Korean hacker, who has officially been charged by the US Department of Justice for carrying out the WannaCry attacks, among other…
British Airways Suffer Data Breach: Website and App Compromised
The customer data of more than 380,000 people have been compromised. British Airways (BA), the largest airline in the United Kingdom,…
DarkCyber: Exploring the Dark Web in Depth
Understanding the dark web has been a complex task for many people. There are a lot of cautions against visiting…
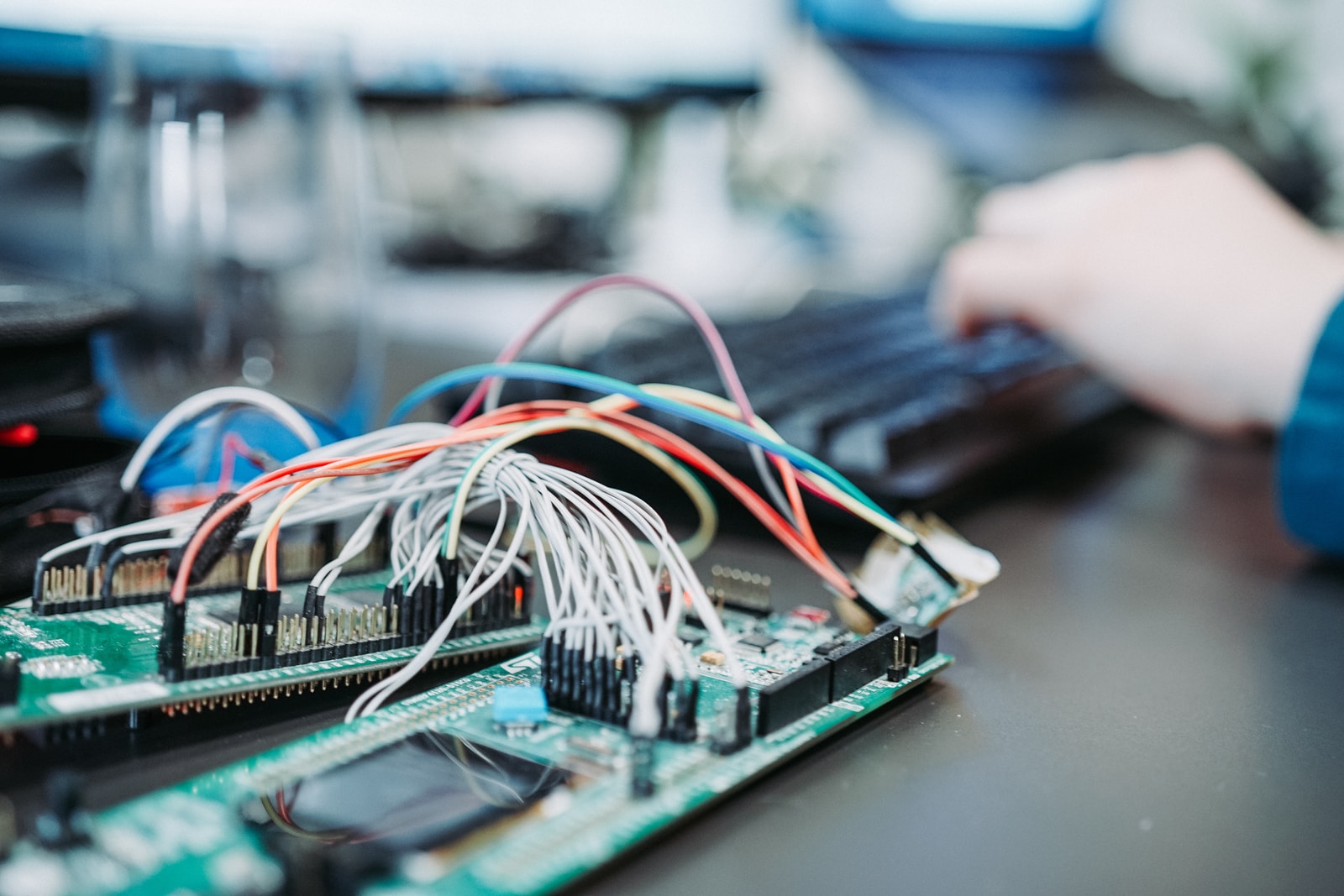
Why IoT is driving demand for Cyber security professionals
The Internet of Things (IoT) is helping bring about more exciting, efficient connected devices for businesses and consumers alike. And…
IFSEC International 2018 announces the Converged Security Centre
IFSEC International 2018 will play host to a dedicated learning and demonstration area, where visitors will benefit from a real-time…
Twitter finds security bug, they advise users to change passwords
Twitter is advising all users to change their passwords. The company said Thursday that it recently discovered a bug that…
More then 5K Gas Station Tank Gauges are Exposed on the Public Net
One gas station failed its PCI compliance test due to security holes in its automated gas tank gauge configuration, researcher…
All about Hydrogen Cryptocurrency
Hydrogen Cryptocurrency (HYDRO) is an innovative blockchain which allows the seamless combination of both current and new personal units to…