Tag: exploit
Top Stories
Critical Cybersecurity Vulnerabilities in Ivanti Products Prompt CISA Emergency Directive
48 Hours to Patch: CISA Warns of Critical Ivanti Vulnerabilities
Cloudflare Halts Record-Breaking DDoS Attack
Cloudflare, a leading web infrastructure company, has successfully thwarted a massive distributed denial-of-service (DDoS) attack, which peaked at over 71…
Ransomware Attack Affecting Thousands of Companies Worldwide
In a major cybersecurity breach, hackers are targeting a two-year-old vulnerability in the VMware server software in a ransomware attack…
Exploiting Advanced Volatile Memory Analysis Challenges for Fun and Profit
Malware continues to advance in sophistication and prevalence. Well-engineered malware can obfuscate itself from the user, network, and even the…
An In-Depth Guide to Network Security
How much do you know about network security? Do you have a high-level understanding of how it works? Do you…
OverRide: Reverse-Engineering and Binary Exploitation Tool
OverRide is a tool help you to explore disassembly, binary exploitation & reverse-engineering through 10 little challenges. In the folder for…
0-Day Vulnerability – How it Works?
A 0day (Zero-day) vulnerability is a software security flaw that is known to the software vendor but doesn’t have a…
Now Available: Exploit Code for the Kubernetes Flaw
The recently disclosed critical-impact bug in Kubernetes created strong ripples in the security space of the container-orchestration system. Now, multiple demo exploits exist and come…
FaceTime group call exploit hits Apple’s iOS 12.1
Newest APPLE'S IOS 12.1 UPDATE doesn't just bring CPU throttling to the iPhone 8 and iPhone X, but also comes with a security flaw…
VPNFilter Malware Adds 7 New Network Exploitation Modules
Security researchers have found even more capable features in VPNFilter, the sophisticated malware that infected 500,000 routers worldwide. Ascribed to…
Peekaboo 0-day – View and Alter Surveillance Camera
Hundreds of thousands of security cameras are believed to be vulnerable to a zero-day vulnerability that could allow hackers to…
Zero-Day Vulnerability Publicly Disclosed By Hacker
A security analyst has openly unveiled the zero-day vulnerability in the Microsoft's Windows OS that could enable a local user…
Critical Flaws In Adobe Photoshop CC
Adobe released security refresh prior to two basic remote code execution vulnerabilities affecting Adobe Photoshop CC for Microsoft Windows and…
New Apache Struts RCE Flaw
Security researcher Man Yue Mo has disclosed a critical RCE vulnerability in the Apache Struts web appframework that could allow…
Banking Malware Uncovered After 5 Years
Security analysts at Kaspersky Labs have revealed another, complex malware that has been focusing on clients of a few Mexican…
New Multi-Factor Authentication Bypass
A weakness in Microsoft's Active Directory Federation Services (ADFS) has been revealed, and can enable hackers to bypass mutli-factor authentication.…
Bluetooth vulnerability Allows MITM Attacks On Varoius Devices
A large number of vendors that have incorporated Bluetooth interfaces with their gadgets without requiring key approval are issuing fixes…
Microsoft Office is Ground-Zero for Zero-Day Exploits
Microsoft Office is becoming a starting point for exploitation is not a challenge anyone wants to win. Tragically for Microsoft,…
Microsoft Zero-Day RCE Bug
Security researchers have found a Windows vulnerability that enables the attackers to execute arbitrary code – and Microsoft hasn't issued…
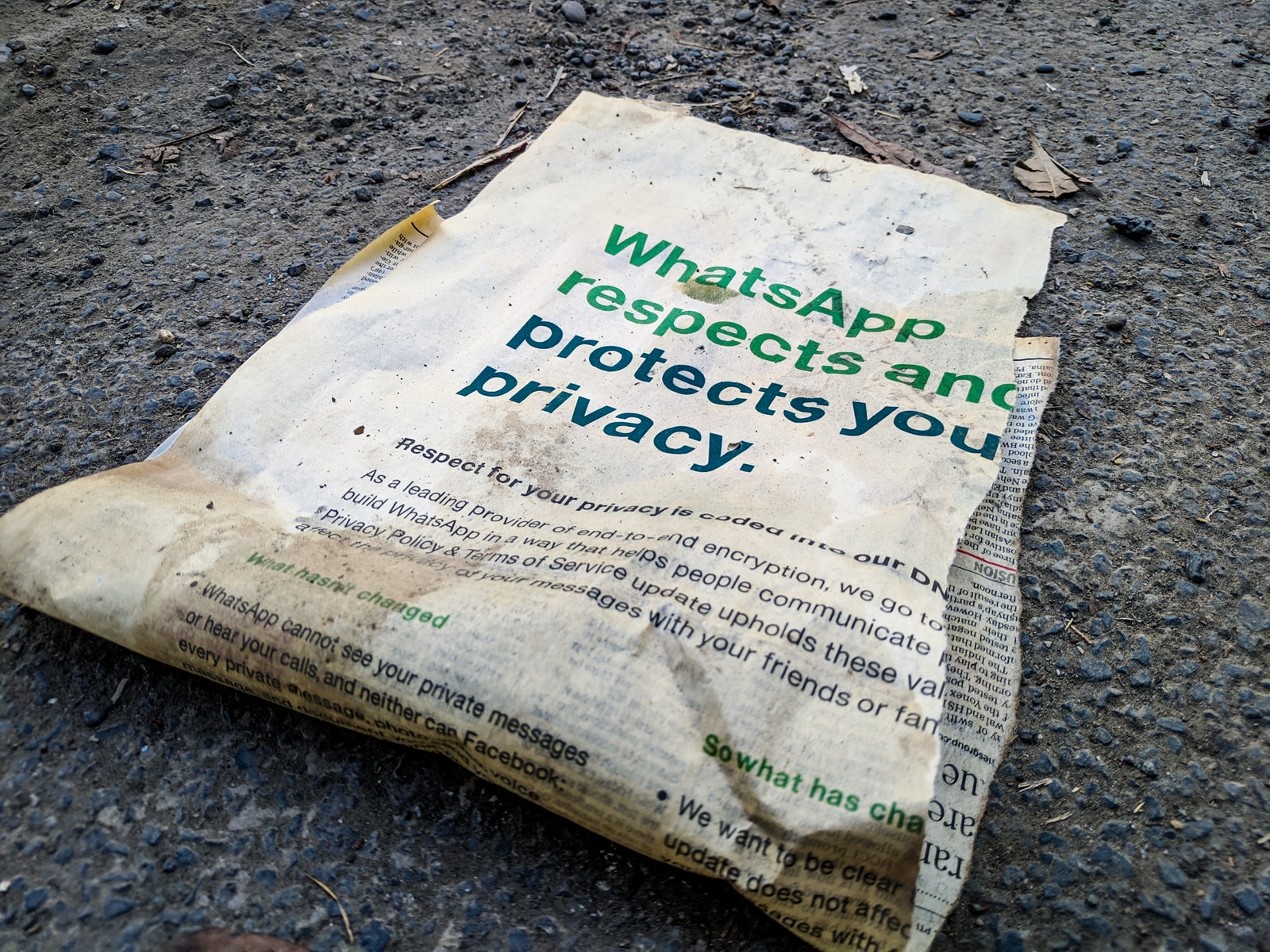
Privacy Menu and Hungry Zeroday Beasts
Privacy has a clearly defined price, and that is shown by the fact that last year certain companies offered up…